Penetration test guide

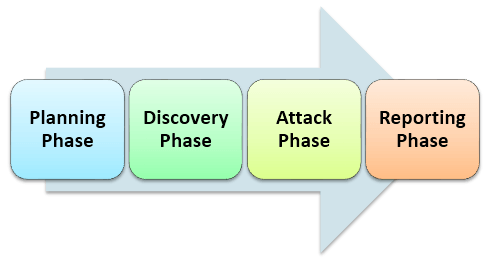
Penetration testing guide - Explained all details like pentest tools, types, process, certifications and most importantly sample test cases for.
Introduction


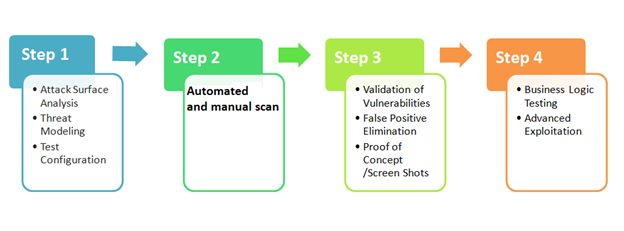


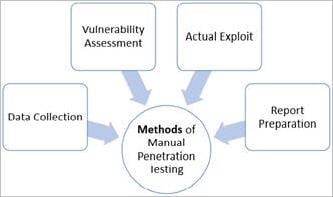
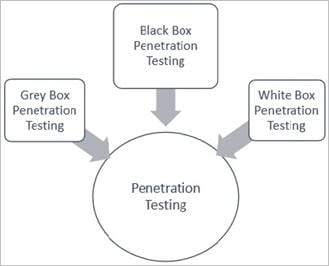
This network penetration testing guide reveals how to use penetration testing tools and best practices for conducting a penetration test.

Emily Age: 35. Hello Gentlemen My Name is Cali,Emails/text anytime but no calls after pm pleaseHi gentlemanAmanda Banks - The British, blonde model escort with a huge appetite for fun and adventure! Open minded and down to earth
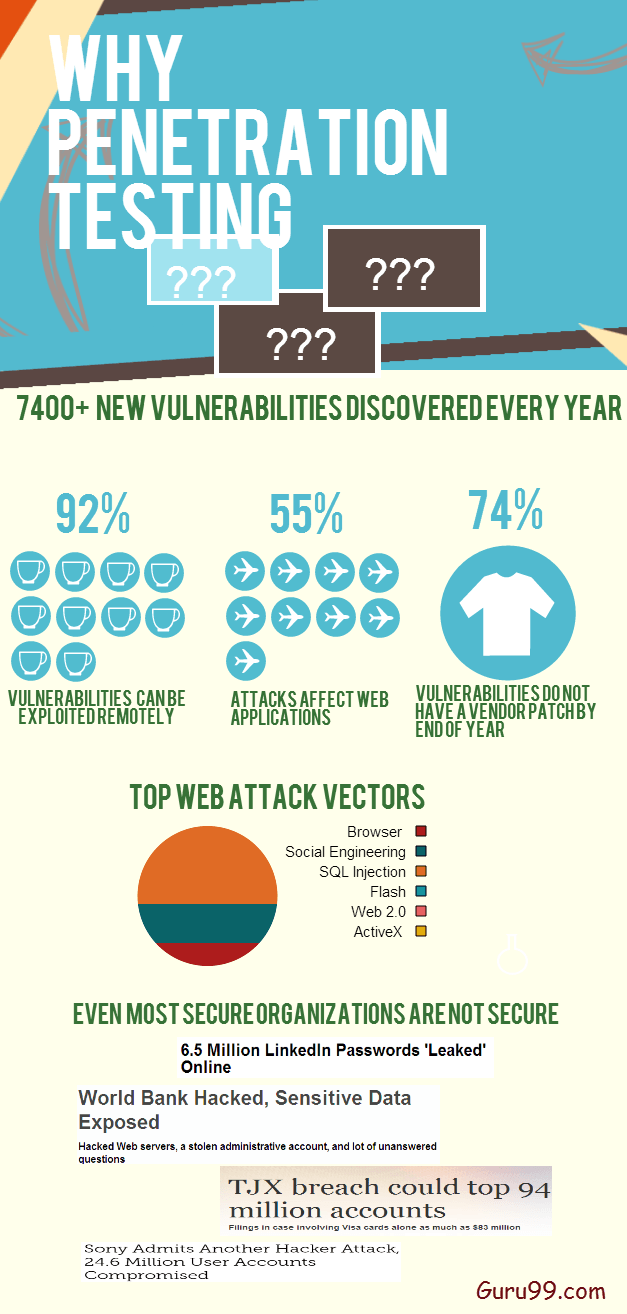

Description:Harpreet Passi Penetration Testing: With such options in hand, the system becomes complex. Since a single person is not handling these things, complete knowledge is impossible. Some teams handle network and create rules on business demand, some handle the configuration part and ensure that the functionality is taken care of; these scenarios leave space for weaknesses. An attacker can identify these vulnerabilities and launch attacks that can do a lot of damage.





























User Comments 4
Post a comment
Comment: